 About ten summers ago, in my role as technology liaison with the Western Massachusetts Writing Project, we were setting up a blog site for our month-long Invitational Summer Institute. This was at the near dawn of blogging, and most of the participants barely knew the word, never mind the concept of online writing spaces. I was just learning, too. We were using a blogging platform called Manila, which had been graciously managed by the National Writing Project.
About ten summers ago, in my role as technology liaison with the Western Massachusetts Writing Project, we were setting up a blog site for our month-long Invitational Summer Institute. This was at the near dawn of blogging, and most of the participants barely knew the word, never mind the concept of online writing spaces. I was just learning, too. We were using a blogging platform called Manila, which had been graciously managed by the National Writing Project.
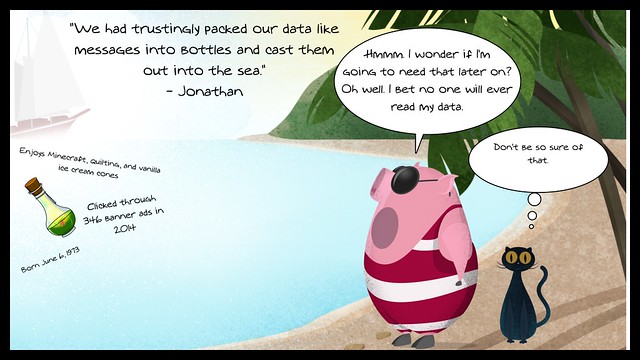
We decided early on to keep our Summer Institute blog closed and private, as a way to help build a sense of trust with our teacher-writers in a space that they didn’t quite comprehend. We wanted the hurdles low for writing and sharing and reflecting. We explained this to our participants, most of whom were relieved that their writing would stay private. I had the idea of taking head shots of everyone and having them all create profile pages as a sort of “get to know you” activity, and everyone agreed.
We set up the pages, which were successful, and then got down to blogging through the summer, and the online writing space was a hit with the institute. Connections were made. Classroom practices were shared. Writing was done. By the middle of the next school year, I had sort of forgotten about the blogging space. As with most summers, even now, once the institute ended, it was nearly impossible to encourage folks to keep on writing. The energy gets lost as the school year looms and our attention turns elsewhere. (which is too bad, but that is mostly the reality).
So imagine my surprise when I get an email from one of the Summer Institute participants, in a tone both angry and confused. This teacher was doing a Google search on herself, and lo and behold, she found the headshot of herself that we had posted in our private space with the promise that the content there would be remain private. She was upset and sort of panic stricken. Even then, I thought she was a tad too nervous (who would search for her image?) but I do not know her whole story (maybe she was hiding from someone) and I was just panic-stricken as the one who had told her things would remain private.
I had broken that trust and it gnawed at me.
I never did find out exactly how the image from the private site spilled into public view, but I suspect it was my own doing, not the site’s. The problem, then as now, is that once the information spills out, it was nearly impossible to stuff it back in. I did remove all the pictures from our site, and even sent a message to Google at the time (and encouraged her to do so) but I know the innocuous nature of a simple headshot would be unlikely to sway Google to move it off its search results. Months later, I could still search her name and still find her image.
I apologized more ways than I can count to this teacher. She never really did accept it, and made it clear that my role as an administrator of the site was a sacred duty, and if I promised something, then I had a responsibility to make sure that happened. Nowadays, we go into digital sites with a little more wiggle room in our expectations, I think. Facebook has done more to erode confidence in privacy issues in social media spaces than any other organization. We are both skeptical of privacy statements from companies and hopeful for the trade-offs.
Most of the participants in the Connected Courses are at the University level, and they have to grapple with the concepts of the privacy walls for their students when they move towards an open platform. If everything is open, how can a student protect their own privacy? Do they have that agency if openness is expected of them? Who is the gatekeeper? The instructor? These very complicated questions require learning about the flip-side of that question: how does one construct a positive digital footprint for yourself that will withstand the possibilities of breaches here and there? This is often one of the important points that Will Richardson makes so eloquently in his various talks and books (including the fantastic, Why School?). His line, not quoted verbatim here, is that when a high school student graduates, they should be able to Google themselves and find a slew of positive data, and our education system needs to do more to help make that happen.
For me, as a teacher of adolescents, it comes down to first making my 11 year old students even aware of the ramifications of their online lives, now and into the future, and we do an entire unit around this concept. Clearly, not enough parents are having those conversations at home with their children. To have choices, you must be made aware of the issue, and be helped along the way to be empowered. Trust between people, and between people and networks, requires awareness of the boundaries of information flow and the places where things might leak out. (Note to movie starlets: don’t take naked photos on your iPhone. Yes, it is despicable that someone hacked your account but what were you thinking in the first place?). We, as teachers, whatever the level, can’t assume our students, even if they are adults, understand this tenet of the digital age we now live in. Assume nothing.
Trust leverages awareness and knowledge, and when that trust is breached — as it was with me and the teacher in the story above — it can be nearly impossible to repair. That teacher never talked to me again, and I wear that responsibility and that memory like a scarf, and I think of it every time I set up an online space for young people and for teachers.
We are potentially entering the age of The Right to Be Forgotten, although I suspect it will be a whole lot difficult that some believe, particularly here in the United States. For me, as a traveler here in various digital realms, I still believe in the Right to Be Remembered, too, and I still think the positives of online interactions outweigh the negatives (call me naive, but that’s what I believe and trust in).
Peace (in thinking),
Kevin

I shudder at the thought of just how many of these types of [somewhat confessional] posts, many of us are going to be moved to write in the future. Thanks for sharing Kevin , I’m sorry your subject never fully forgave you.
What my students don’t quite understand, because they can’t quite wrap their heads around it, is the permanence of things on the net. We have long discussions about sharing of images, in particular, as Instagram is still big with them. Much of the discussion centers on the obligation of the sharer to think not just about themselves, but about those who are in the pictures with them.
You might be interested in this:
http://www.kryogenix.org/days/2014/09/30/the-next-big-thing-is-privacy/
Thanks, Paul. I will give it a read.
I think that online privacy is a multidimensional issue. The most disturbing aspect, in my opinion, is the loss of control from the big names – Facebook, Google, etc. The fact that Facebook changes privacy settings so often without providing information is an example. Google searches being filtered for individuals – that’s a concern.
On the flipside, as you say, if we don’t teach young people how to manage their online identity and information, they will also be missing out on the benefits of a sensibly constructed online profile which is potentially part of their professional curriculum vitae.
And although, as you say, once you put something out there you can’t take it back, there is also the reality of not being found or read when you want to be. When my year 9 or 10 students worry about their blog posts being read by ‘the world’, I also tell them that it is likely they will not be found unless I share them with my networks – and building such influence as to have confidence in having your shared material read is a lot of work and takes time and ongoing committment. If you look at the stats of an unpromoted student blog post, you will find virtually no readership and therefore no visibility.
Thanks for raising so many issues about privacy, Kevin.
It is a conundrum, right? Something may be permanent, so be thoughtful, but then when they are thoughtful, it might just get lost in the mix of the world and never get read. Interesting dichotomy of ideas ….
We are guilty too. Absolutely everyone falls in the same trap of jumping on new bandwagons without being critical of them. It’s worse when we force our students to do it (because students can’t oppose to it). It’s worse when our institutions force us to force our students (because few instructors will oppose it, and few students will further oppose their instructors if it is institutional).
An important issue, and the biggest problem I see is the way Fear-Uncertainty-Doubt keeps people from even exploring solutions at my school. The way address this important issue is to use tools that the students control, making sure they know how to choose the options they want. Do they want their name, or a pseudonym, or no name at all to appear on their blog and on their project website? Do they want to use a personal photo or some kind of other image instead? (I always use an animal avatar so they know it is totally fine with me not to use a personal photo.) Do they want to leave their work online after the class is over or delete it? By using tools where the students are in control of all those important decisions, and by knowing how how to use those tools (I make sure to provide tutorials on all these options), it’s not so much about trusting me or not (I want them to trust me but, hey, they only know me insofar as I am their teacher for one class) … instead, I want them to understand how to use the tools they have, making good choices, and also thinking about the choices they make for tools that have nothing to do with class.
Choosing the right tools.
Teaching how to use the tools.
Encouraging the students to trust themselves.
Spreading knowledge, not FUD.
That’s how I see my role.
Since my only teaching experience in the Internet age is with college students, I don’t know how far that can generalize in K-12.
And… I am pleased to note… well over 95% of my students choose to leave their class project online, for which I am very grateful!
Laura
Your comment reminds us all of teaching “agency” when it comes to technology, and harnessing the possibilities for our own goals and needs and aims.
Kevin
I tried to show how FUD can be fought back at this post:
http://paulolivier.dehaye.org/posts/security-theatre-in-airports-and-academia.html
It ties the physical and digital worlds.
Another very thoughtful piece–and a wonderful addition to the continuing conversations we’re having through the Connected Courses MOOC (#ccourses). Hope this becomes another required reading for anyone interested in issues of privacy (and lack thereof) on the Internet. It’s also a great reminder that if we don’t want to see something on the Internet, we better not put it there.
Paul
Thanks for being a regular visitor here, and leaving comments.
Kevin
Interesting question.
Provocation n•459
Do people freak out when they are seen/recognised in a street?
Do people worry about how they will be remembered?
Hmmmm .. provocative questions (as expected, my friend).
Some people do:
http://cvdazzle.com/
Problem is that they would be ridiculed, but I can see it happening in a dystopian future.
Kevin, this a very beautiful post and I thank you for that. It made me think about the inevitable imperfection of what we might ‘teach’ about privacy and how to manage it. To me privacy is a relational practice. Since time immemorial, privacy has been breached by the betrayal of (perceived) confidence by human beings. Technology adds the dimension of non-humans betraying our confidence, whilst offering us seductive opportunities for creativity.. For me, it is about teachers and learners learning side by side about the dynamic nature of tech services operation of privacy. This requires a balance of caution and joy – not succumbing to fear – not being blind to risk. The question is what roles do teachers have in supporting their students in their joyous use of technologies whilst helping them make their own decisions about risk management. I made this comment on Dave White’s blog post http://daveowhite.com/jisc/disconnected/
“So this learning about learning could be a mix of explicit and implicit but I think the challenge for teachers is contributing to this and supporting it whilst still learning about it themselves. Well, I have always found it a challenge, anyway;)”
Frances
The “balance of caution and joy” seems to capture the concept here, right? Yes, we could just say,”So long digital world” and keep everything private. But the reality is that we would be missing out on so much, from learning situations to connections across the globe to expanding our own “echo chambers” so that we hear other voices (although I know the net can also provide narrowing tunnels, too).
Thanks for writing
Kevin
I agree with 99% of what you wrote here and think of it frequently in conversations with my daughters (ages 11 and 7). Recognizing the permanence of things online is critical and, in general, we aren’t doing a great job of helping kids do so.
That said, I take issue with your side note to movie starlets. Nothing about such exploitation is the fault of the person being exploited. I agree with the recommendation not to have such photos on their phones. It is simply too risky. However, should some choose to do so and their phones get hacked – that is not their fault.
Hi Jenny
Yes, we need to do more, as parents and teachers. And I was not blaming the stars for having their phones hacked. I was making the point that we prob should expect/anticipate that it might happen, and act accordingly.
Thanks for taking the time to comment.
Kevin
(Intoning my best Bill Clinton voice)- Kevin, I feel your pain.
You had every best intention out the outset because you controlled the information, but alas the controls themselves are imperfect. It might have been a database gaffe or a permissions issue.
Yet, the idea of absolute guaranteed privacy is not really possible. Everything we think of as private in an online space is potentially not.
What we think of as secure, private information is always always always, even if low, risk to be broken open. And we make a mistake when we think we are giving people “secure” places. The only secure places online are not online. Period.
The hindsight lesson and for others, is careful consideration (and this is not an accusation, I likely made similar promises) of what we are asking of people to do online. The bottom line for me is always the individual must get to choose, armed with proper information, what of themselves to place online. Like Laura suggests, give people options to use avatars, pseudonyms.
A right to be forgotten seems reasonable, and I can extrapolate circumstances when I direly would want that. But it works against the principles of how the open internet works. For all we cherish of openness, there has to be the potential for the counter opposite. You cannot have one w/o the other.
So I would opt for rather than a hope to be erased, is to be an activate producer of my own self, that what I can say as to my positives can outweigh, those past blips.
I am, a silly idealist.
Pure privacy, online, the only full protection are the ones we directly control. At the first giving of information to someone else, we put that on the table.
I hear your voice!
🙂
I think “careful consideration” is key to any instructor moving in this direction, and also, being as upfront as possible, too. Yes, I am like you — the idealist — and see the positives as far outweighing the negatives. When something happens to offset that balance, it makes me think, and then plan accordingly. I guess everyone is always learning.
Kevin
Kevin, thanks for a great post. Trust, assumptions, permanence, self-determination, and the value (both personal and economic) of information: it’s a heady mix. Students are already generating massive data trails well before they’re first introduced to even rudimentary notions of info literacy. We’ve traditionally recognized the necessity of teaching students how to comport themselves effectively in various spaces – the physical classroom, the dialogic “space” of literary or academic written discourse, public policy conversation, the research community, etc. Understanding the mechanisms of online presence, interaction, and communication is as necessary to truly effective critical interaction as understanding, e.g., the patterns governing how economics influence politics.
I agree with M. Cogdog. If u don’t want to ‘lose control’ of data throw away phone, pc, passport, driving licence, credit card, don’t go anywhere with cctv, maybe New Guinea in a cave might work.