 (Warning: this is a bit of a ramble)
(Warning: this is a bit of a ramble)
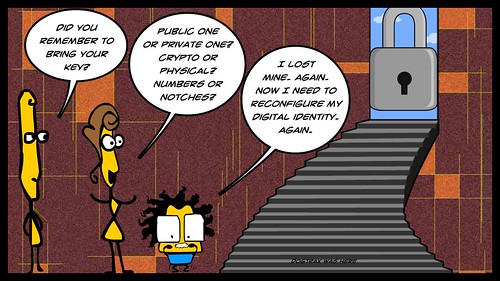
In EL30 (E-Learning 3.0), Stephen Downes has us now thinking beyond notions of identity, and into the future of digital authentication.
Stephen, our navigator, explores the notion of private and public ‘keys’ as a way to keep our identities and our data private, and firmly in user control. As I understand it, the encrypted private key is what we would use to access and share our information and the public key is the doorway that others can enter if they have a matching or designated encrypted private key themselves. Anyone else, without that key, would not be able to move into the encrypted data.
The keys — private and public — create a barrier, or a wall, of protection, and only those who we trust and know would have access, even if it were leaked or hacked or whatever. In this case, he is talking about how to protect our identities, and perhaps, how our Identity Graphs might reflect this kind of protective barrier.
I’m wondering, how does the use of encryption keys form our online identity? I also wonder, given the nature of open connectedness that informs so many of the educational and learning circles I am part of, how does this shift to extreme privacy both enhance and hinder those interactions? Will people who might otherwise be important to my own learning be left out of the loop, if the door is locked too tight? I have this analogy in my mind — which is not quite apt — of how comments on blogs are sometimes set with spam filters so high that one gives up on even bothering to take time to leave a comment, ending a conversation before it even begins. Would encrypted keys do the same, but even more so? I don’t know enough about this topic to say with any authority but I wonder about it.
In one case, Stephen describes a key that is literally a small drive that you plug into computers you want to use, and your login and data trail is on the device. This device you take with you (on your keychain, perhaps), so that you no longer rely on browsers as your login point (and therefore, risk leaving data trails for others to find and use).
As I mentioned, I don’t know much about this encryption process, although I have read a little bit about it before and wondered how technology solves a problem technology has made (privacy issues), but does one technology fix of another technology problem then somehow open the door to yet another unforeseen technology problem? What problem might encryption keys pose? Maybe I am just being cynical. I sure don’t have an answer to this problem of identity hijacking by hackers and marketers and technology giants and more.
Take a listen to Stephen and see what you think. The comic above was my attempt at humor — of noting that whatever the technology, someone is sure to lose it.
Peace (ID it),
Kevin
Before the big players pushed us to encrypt everything (see Dave Winer here http://this.how/googleAndHttp/ ), encryption was just the less important sibling of the Siamese twins of authentication and secrecy: The only reason for me to use secrecy was to keep my password (or private key) secret because otherwise authenticating would not be meaningful. But the two are technically intertwined and guarantee maximal confusion, in particular because the terms ‘public’ and ‘private key’ are so unfortunate. Think of the private key as a kind of password, just that you don’t need to send it across the web.
Thanks.